


Cyber incidents don’t always begin with a hacker targeting your systems directly. More often, they start with a trusted third party, a vendor, a SaaS tool, or a contractor who has access to your data, your systems, or your customers’ information.
That’s the conversation Xigent’s CISO, Amos Aesoph, and the team at North Risk Partners sat down to have, and the result is something that every business leader should read, not just your IT department.
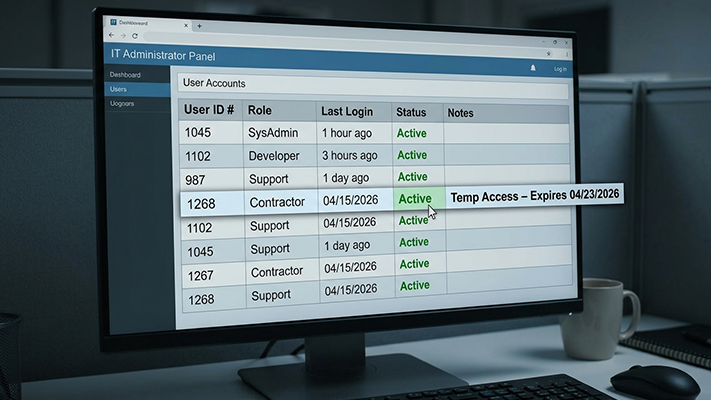
We’re talking about the smaller SaaS tool that three people on your finance team adopted last year. The regional IT firm that still has remote access to your systems. The contractor who needed temporary credentials that were never revoked
None of those feel like “cyber risks.” Until they are.
What we’ve seen is that risk doesn’t follow your budget. It follows your data. And the organizations that get ahead of third-party risk are the ones who stopped asking “how much do we pay this vendor?” and started asking “what can this vendor access? What happens if they’re compromised?
After working through this with North Risk Partners, there are five ideas we keep coming back to:
Employees are picking up AI tools at a rapid pace. Most of those tools haven’t been vetted, and some are quietly touching data they shouldn’t be near.
At the same time, phishing and social engineering attacks have gotten harder to spot with AI-generated emails, voice cloning, and deepfake videos.
Vendors rely on the same underlying platforms. A failure in one shared infrastructure provider can quietly take out multiple vendors at once. You might not even realize you have that concentration risk until a breach happens.
Here’s the approach we’d suggest:

Cyber underwriters are paying close attention to how organizations manage vendor risk. What they want to see are actual controls, such as multi-factor authentication, managed detection and response, and documented vendor risk management processes.
SOC 2 reports matter, but they’re a starting point, not a finish line. The organizations that get the best coverage terms are those that can show their work.
If any of this is prompting questions about where your organization stands, feel free to reach out to the Xigent team or connect with North Risk Partners Risk Advisors.
We’ve also put together a one-page summary you can share with your leadership team. Download the summary here.
Identify your vendor risks before they become breaches. Contact Us to assess your exposure and strengthen your security strategy today.
Xigent | In collaboration with North Risk Partners